Why What You Learn in Class Matters: Handpicked Real-World Problems
Introduction
In this blog post, I’m highlighting three problems I’ve had the opportunity to work on. I found their solutions both endearing and instructive, especially for a wider audience such as Computer Science or Software Engineering students. Feel free to try solving them if you haven’t already. The first one is a great warm-up for Advent of Code (and Open Day 😉).
1. Groups in Groups
Problem Statement:
One system allows a specific user group to be part of another group. If Group A is a subgroup of Group B, then Group B cannot be a subgroup of Group A—not even indirectly (e.g., A → B, B → C, C → A). The task is to display the parent relationship of a selected group.

Solution:
You may have seen similar structures in a filesystem GUI or encountered recursion in OS lab exercises involving file system entries. This problem, like many others, can be solved using one of the most versatile algorithms: Depth First Search (DFS).
How do we apply DFS here? One key observation is that there must be at least one group that isn’t a subgroup. Why? Let’s use an intuitive explanation (powered by GPT) alongside formal proofs:
No Two Boxes Can Contain Each Other at the Same Time
Think of a group as a box. Some boxes can contain other boxes.
Rule: No two boxes can contain each other at the same time.
Now ask yourself: Is it possible that every box is inside another box?
Pick any box.
That box is inside another box. That box is inside yet another. Keep going.
You can’t ever return to the first box you picked (the rule forbids two boxes containing each other).
But there are only finitely many boxes.
So eventually, you must reach a box that is not inside any other box.
That box is the “top-level box”—the one that belongs to nothing.
Starting from these top-level groups, we run the DFS and track which nodes are being visited. Suppose we have paths like:
[[1, 2, 3], [1, 2, 4], [1, 3], [5, 3]]
Filter out all paths that don’t include the selected group. Sort by ID and then by length:
[[1, 3], [1, 2, 3], [5, 3]]
Print the first path. For the second path, remove the matching prefix and print from there. Repeat until the end. Boom! We’ve solved it (and documented the solution 😄).
2. Big-Endian to Double SQL Migration
Scenario:
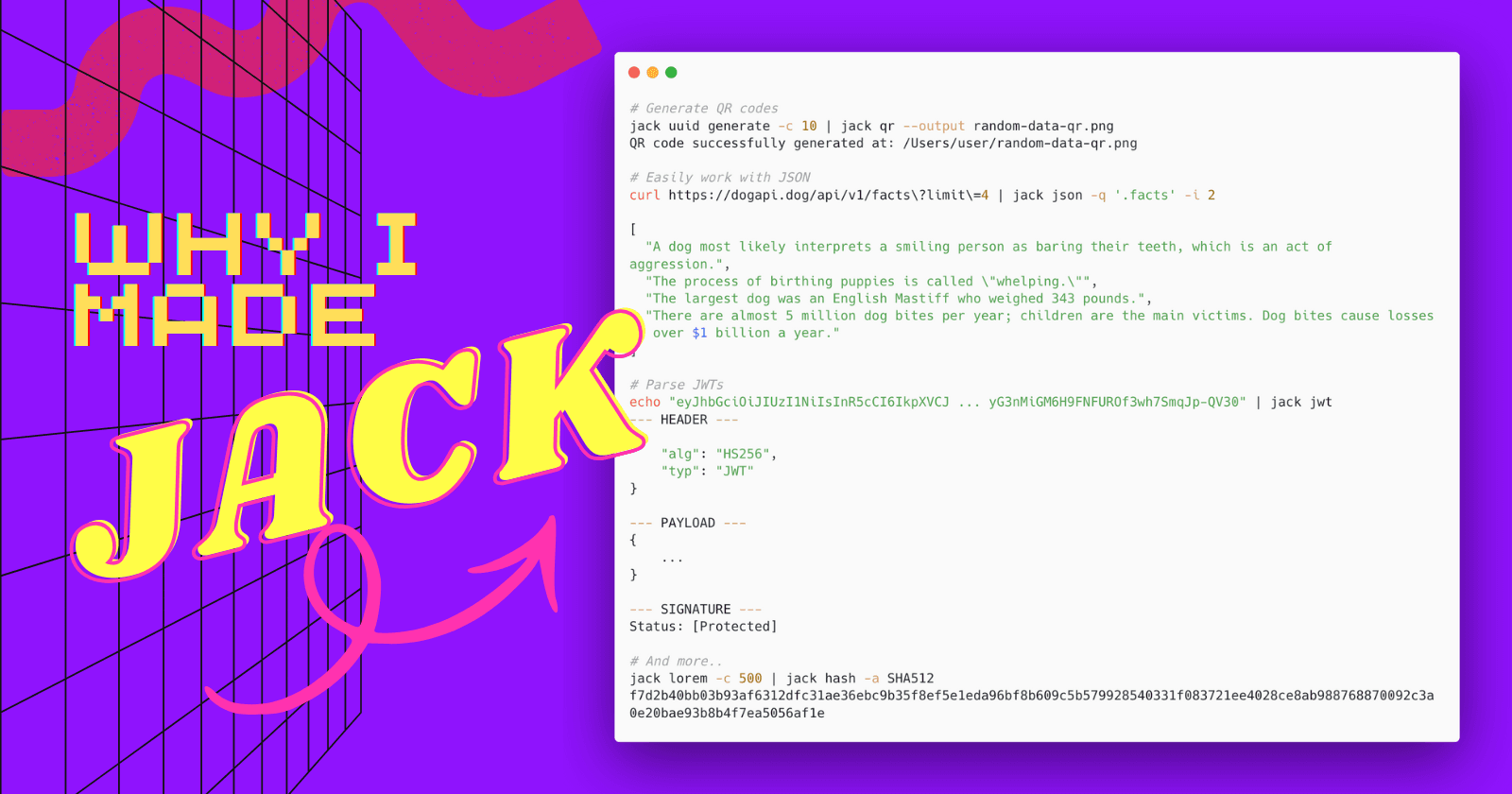
Imagine you have a relational table named vector containing arrays of N positive double numbers stored as big-endian hexadecimal representations, along with a column type (e.g. position). For your favorite 3D position vectors, you need to store additional data beyond (x, y, z), and the dependencies require creating a separate entity. The constraint: solve it using SQL* (MySQL in my case). Any SQL nerds?
Example:
| Value (Decoded) | Value (in SQL) | Type |
| [23.19191, 35.132, 380.77] | 40374c8f5c28f5c34041b851eb851eb840877b3333333333 | ‘position’ |
| [0, 11, 450] | 00000000000000004026000000000000408c400000000000 | ‘position’ |
Solution:
This might not be the cleanest solution, but I chose this challenge because IEEE 754 representations are essential knowledge for computer architecture classes, SQL, and data migration stress. Hopefully, this blog sheds light on the question many engineers ask: “Where would I need this knowledge?”
Start by selecting all rows where type = 'position':
SELECT value FROM vector WHERE type = 'position';
Next, split the concatenated value (each double is 8 bytes = 64 bits):
SUBSTRING(value, 1, 8)
SUBSTRING(value, 9, 8)
SUBSTRING(value, 17, 8)
Create a function to convert each CHAR(16) hex value (16 hex digits = 64 bits):
CREATE FUNCTION convert_big_endian_to_double(big_endian_hex CHAR(16)) RETURNS DOUBLE
Convert the hex to binary:
SET binary_representation = LPAD(CONV(big_endian_hex, 16, 2), 64, '0');
Then decode using IEEE 754:
How do we convert? https://en.wikipedia.org/wiki/Double-precision_floating-point_format

DECLARE result DOUBLE;
SELECT
POW(-1, CONV(SUBSTRING(binary_representation, 1, 1), 2, 10)) -- sign bit
POW(2, CONV(SUBSTRING(binary_representation, 2, 11), 2, 10) - 1023) -- exponent
(1 + CONV(SUBSTRING(binary_representation, 13, 52), 2, 10) / POW(2, 52)) -- significand
INTO result;
And that’s it! You can return the result from the function; however, keep in mind edge cases such as zero, infinity, etc.
3. Finding MAC Addresses of Disabled Network Adapters on Windows 7
Problem:
This is a bug fix, not a feature request. Not strictly tied to uni classes, but I chose it because it’s an unusual, non-trivial problem that requires deep troubleshooting across shells, WMI, and the registry.
How do you figure out the MAC addresses of all (including disabled) physical network adapters on Windows 7?
Solution:
It sounds trivial, but it’s not. Disabled physical adapters don’t expose their MAC addresses via standard WMI queries, and Get-NetAdapter isn’t available on Windows 7. If you’ve used WMI queries before, and the user has a disabled network interface, you won’t get the MAC address.
You might be able to resolve this with some Windows 7 upgrades (if you have hardware control). Otherwise, the only solution I could propose is to ask the customer to enable the interfaces or upgrade. ¯\(ツ)/¯

(My Ethernet 2 was intentionally disabled)
Final words
Knowledge-sharing is one of the foundations of community progress and personal growth for those who share it. I’m grateful to CodeChem and its clients for fostering a culture of knowledge sharing and accessibility. I hope this blog post serves as my contribution to that spirit. If you find this blog post useful, certainly do let me know, and I will share more!